Take Your Linux Monitoring To The Next Level With eBPF
earn how eBPF offers a powerful way to monitor network traffic and execute actions based on specific conditions, offering a secure and reliable way to extend kernel capabilities.
If you want to take your Linux system monitoring and performance diagnostics to the next level, consider using eBPF (Extended Berkeley Packet Filter).
This powerful tool provides you with an unprecedented level of visibility into what is happening inside your systems. With eBPF, you can gain insight into resource usage and identify potential issues in real time. It's a great solution for quickly troubleshooting problems and implementing performance improvements.
In this blog post we'll look at what eBPF is, what it can do for you, and how to get started setting up specific use cases. Read on to unlock the power of extended BPF!
What is eBPF in Linux?
eBPF (extended Berkeley Packet Filter) is an in-kernel virtual machine that provides a generic and powerful platform for network monitoring, security analysis, and traffic control within the Linux kernel. eBPF provides the capability of executing user-defined programs directly in the Linux kernel without the need for recompiling the kernel space.
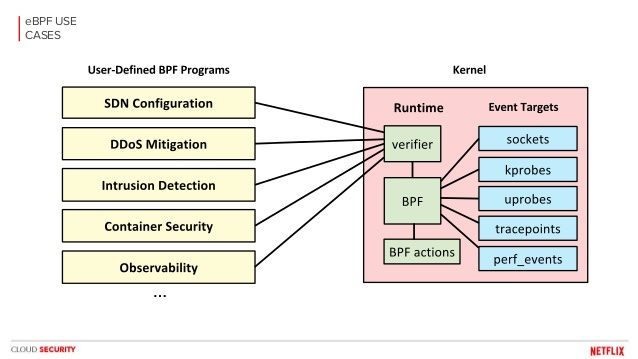
This feature allows for better performance and complexity when dealing with tasks such as packet filtering, logging, tracing,system calls, and more. It also provides improved scalability and flexibility compared to traditional solutions such as iptables. The potential of eBPF is immense and can be used in various applications ranging from network performance monitoring to intrusion detection and security systems.
With its impressive ability to provide low-level access to kernel space data structures, eBPF is currently being adopted across a variety of organizations looking to improve their network infrastructure.
What Linux kernel supports eBPF?
The Linux kernel that supports eBPF (extended Berkeley Packet Filter) is the 4.1 version and above.
It is part of the Linux kernel's in-kernel virtual machine, which allows for the execution of sandboxed programs in the kernel context. This enables a wide range of uses, such as networking and security monitoring, kernel tracing, system call tracing, and debugging. The eBPF programs can be used for packet filtering, network performance analysis and profiling, traffic control and manipulation, as well as various types of hardware performance measurement.
With eBPF support enabled in the Linux kernel, developers and administrators have been able to leverage this powerful technology to gain greater visibility into their systems and improve upon existing functionality.
What is the difference between eBPF and BPF in Linux?
eBPF and BPF are specialized programs for the Linux operating system.
Both technologies provide a secure and efficient way to interact with the Linux kernel, but they have significant differences in their respective implementations.The main difference between eBPF and BPF is that eBPF is an extended form of traditional BPF, which extends the capabilities of BPF to allow it to run more complex instructions.
eBPF linux provides additional features including attaching programs to specific events in the kernel space and running sandboxed programs without the need for privileged access. Additionally, eBPF has a virtual machine that allows running applications within the linux kernel space, while still providing security against malicious code or accidental errors.
Furthermore, eBPF's dynamic tracing feature allows developers to track changes in system resources such as memory or CPU usage at runtime. It can also be used for data collection and analysis, making it much more versatile than BPF.
What programs use eBPF?
eBPF (extended Berkeley Packet Filter) is a powerful and versatile in-kernel virtual machine.
It has been steadily gaining popularity over the past few years due to its ability to provide users with low-level packet filtering and network traffic analysis capabilities. eBPF is used by many different programs, such as system administrators for security monitoring, developers for debugging, performance tuning, and even by system architects for virtualized networking solutions.
For example, Linux developers have used eBPF programs to allow user space applications access to the networking stack of the operating system. This provides flexibility and control that was previously not available and allows for greater scalability when dealing with large networks or services.
Additionally, several cloud providers are now offering services that leverage eBPF capabilities such as Amazon's X-Ray service which uses it for distributed tracing or Google's Cloud Data Loss Prevention which uses it for data privacy.
What is eBPF and why does it matter for observability?
eBPF (Extended Berkeley Packet Filter) is a Linux technology that enables efficient programmatic packet processing and monitoring.
It was designed to allow programs to be written in user space, which dramatically improves performance and makes the system much more extensible. eBPF has become increasingly popular for observability and offers a wide range of functions like network tracing, monitoring, security analytics, ingress/egress control, system calls, etc. eBPF allows for the creation of custom filtering rules that can capture data from within the kernel space at a much higher level of detail than traditional packet filters.
eBPF can also be used in conjunction with other technologies such as tracing frameworks, logging systems and analysis platforms to provide comprehensive visibility into an application's behavior and performance. This makes it possible to quickly identify problems or gain insights into the underlying architecture of an application.
Finally, because eBPF runs inside the kernel, it can provide more detailed information about network activity than any other approach.
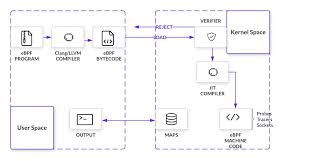
How is eBPF implemented?
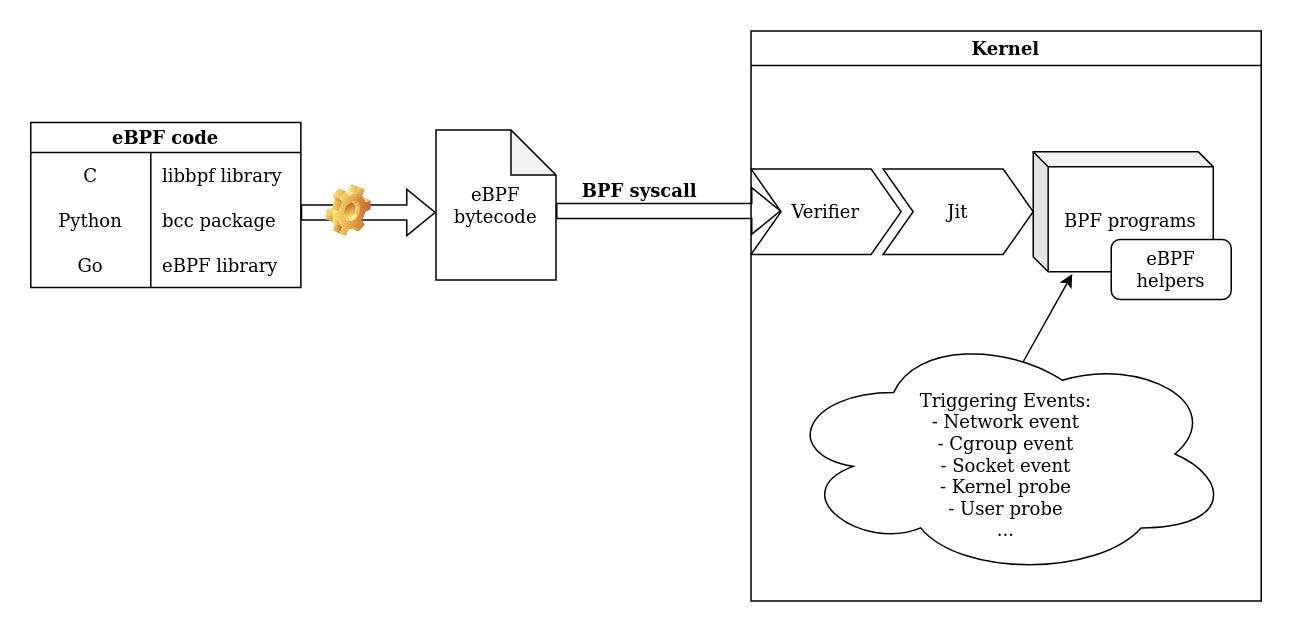
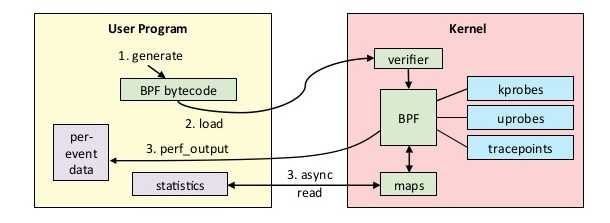
The eBPF system consists of three components: a verifier, a register file and an interpreter.
The verifier checks for syntactic correctness and bounds the execution time of BPF programs; it also performs static analysis to ensure that the program does not have access to sensitive data or exceed its allocated time limit.
The register file holds program state variables such as stack pointer, program counter and other relevant data needed by the interpreter during execution. Finally, the interpreter reads from the register file and translates BPF instructions into native x86_64 instructions before executing them in-kernel.
Since its introduction in version 3.18 of the kernel, eBPF has been rapidly adopted by developers due to its versatility and performance benefits over traditional system tracing tools such as SystemTap or DTrace.
What is the difference between XDP and eBPF?
XDP and eBPF are two powerful tools for network packet processing in Linux.
XDP (eXpress Data Path) is a programming framework that provides an extremely fast networking layer for data analysis, manipulation and filtering of packets at the lowest possible layer, which is the driver level. Bypassing the kernel layer, XDP can reduce latency and increase throughput compared to kernel-level solutions. XDP works by providing hooks into the hardware through drivers and allowing user-space programs to directly access hardware resources with minimal overhead.
On the other hand, eBPF is a Linux technology that can be used to hook into several different subsystems in the kernel function order to monitor or manipulate system behavior from user space.
It works by attaching small pieces of code called “programs” to specific events inside the operating system, enabling users to customize their systems’ behavior without having to write kernel modules. eBPF programs have direct access to all kernel data structures, allowing them to make decisions on how packets should be handled or modified.
The main difference between XDP and eBPF is that while XDP works at a lower level than eBPF (the driver level), it does not provide much flexibility when it comes to modifying packets; instead it focuses on providing high performance packet processing capabilities.
What is eBPF virtual machine?
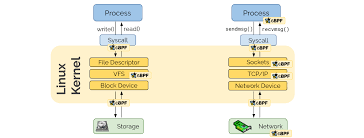
eBPF (Extended Berkeley Packet Filter) is a virtual machine that runs in the kernel space, allowing direct access to kernel internals and providing more control over packet processing than traditional solutions like iptables.
eBPF provides the ability to write custom programs that can be attached to different parts of the network stack, such as sockets and networking devices. These programs act as filters filtering network packets and are used to inspect, monitor or even modify data before it reaches its final destination.
The eBPF virtual machine gives developers an unprecedented level of control over how incoming packets are handled by their systems, fundamentally changing the way in which system administrators can secure their networks.
In addition to security benefits, applications built with eBPF also often increase performance due to increased flexibility and lower overhead from not having to rely on additional user-space processes.
Can eBPF crash the kernel?
No, eBPF does not crash the kernel.
Instead, it is a safe and secure technology that is built into the Linux and used to extend its functionality through small programs called “programs” or “filters.” It offers a powerful way to monitor and filter network traffic as well as execute arbitrary actions based on certain conditions, such as modifying network packets or tracing system calls.
Additionally, eBPF provides a sandboxed environment to ensure that any code it runs does not affect the OS integrity, thus preventing malicious code from crashing the system. Furthermore, eBPF programs are validated before execution in order to rule out any potential errors or conflicts with existing kernel functions.
As such, eBPF can be considered a stable and reliable technology for extending the capabilities of the kernel without increasing its attack surface.
What kernels support eBPF?
The majority of Linux distributions have supported eBPF programs since version 3.18, including Ubuntu, CentOS, openSUSE and Debian.
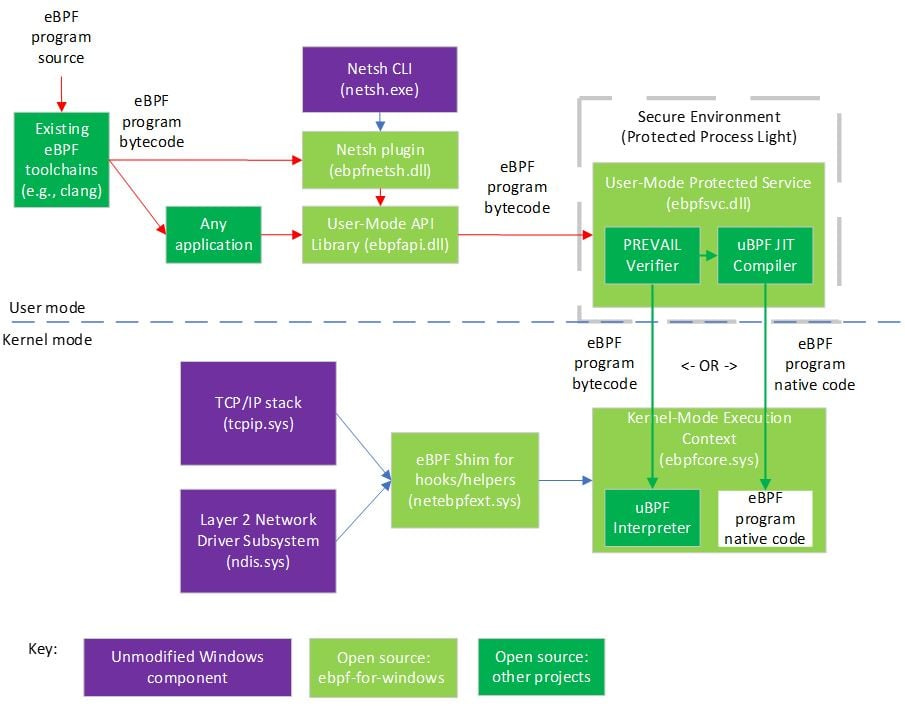
The mainstream Linux versions that support eBPF are 4.1 and later, with much improved functionality compared to the 3.18 version. Additionally, Microsoft Windows 10 also includes support for eBPF in its latest release. Furthermore, some other operating systems such as FreeBSD or macOS are also expected to include support soon due to the growing popularity of the technology.
As a result, the use of eBPF is becoming increasingly widespread across cross-platform compatible systems.
Is eBPF a kernel module?
eBPF (extended Berkeley Packet Filter) is a virtual machine that runs inside the Linux kernel.
It is a powerful tool for monitoring, tracing and filtering operations within the system. In addition to being able to access kernel functions, eBPF can also run user-space code through its associated kprobes interface. This allows users to create custom programs that run inside the kernel and have direct access to data structures in memory.
Consequently, eBPF programs can be used to solve a wide variety of problems ranging from network performance optimization, auditing and security enforcement. It should be noted, however, that although eBPF runs within the kernel it is not considered a kernel module itself but rather an in-kernel technology exposed via system call APIs.
What is eBPF kernel code?
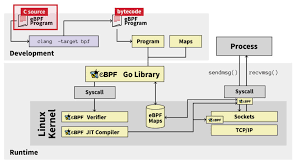
eBPF (extended Berkeley Packet Filter) is a low-level, in-kernel virtual machine that allows for the execution of custom programs inside the kernel.
It was designed to enable increased control over network and system operations within the kernel while maintaining its security. eBPF programs can be used to modify kernel behavior or add new features, such in kernel helper functions such as implementing firewalls, tracing applications and performing in-kernel analysis of network traffic.
These programs are loaded into the kernel at runtime from userspace and executed by eBPF virtual machines.
Unlike other uses of virtual machines, eBPF programs does not require a separate binary to be compiled for each platform; instead it uses just-in-time compilation techniques that allow for code portability across different architectures.
eBPF has revolutionized the experience of Linux monitoring.
It enables efficiency, security and performance in ways that weren't accessible before. With its intuitive way of collecting data, eBPF allows for new levels of insight in real-time system monitoring. There is no doubt that taking our Linux monitoring to the next level with eBPF will provide us with improved visibility and deeper understanding of our system performance. If you are looking for a comprehensive solution to your monitoring needs, eBPF is definitely your best bet.
In addition to this, it also provides a scalable path to scale your operations when necessary without having to modify existing code or systems.